Antwort What is OWASP dependency-check? Weitere Antworten – What is dependency-check scan
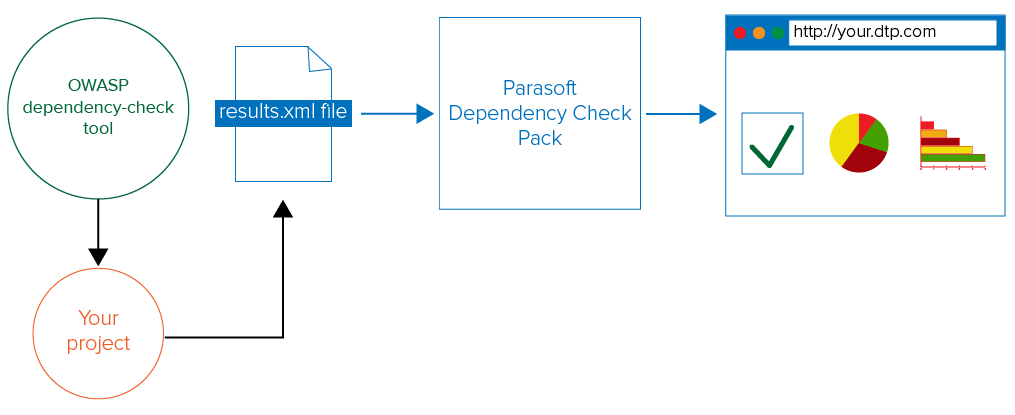
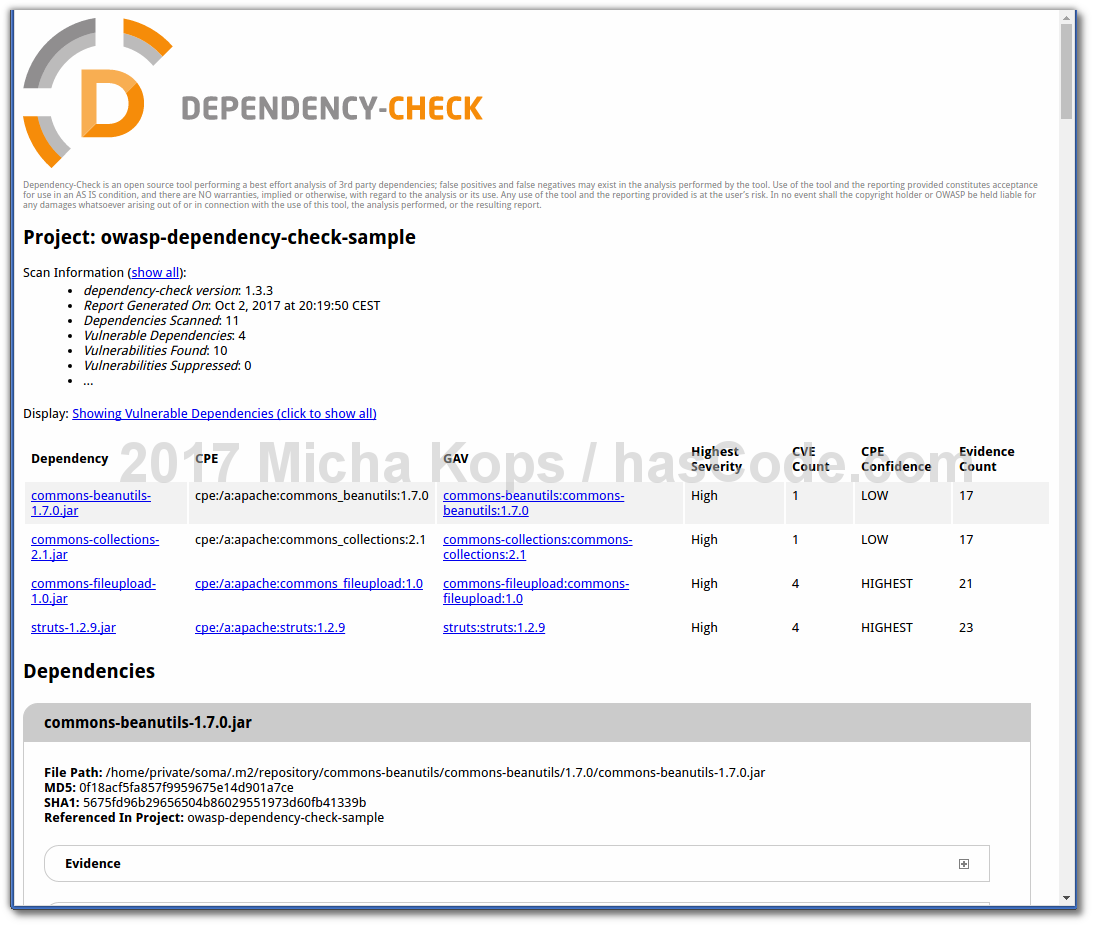
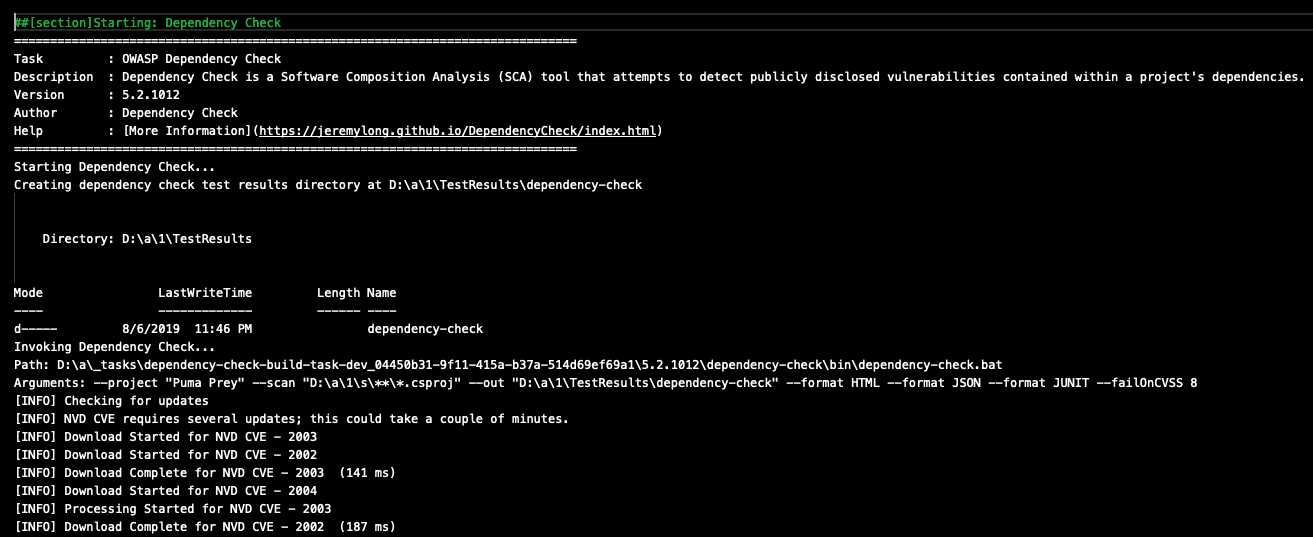
OWASP Dependency-Check is a Software Composition Analysis (SCA) tool that actively scans through a project's dependencies to detect and report on publicly disclosed vulnerabilities, thereby improving application security. Open source projects often suffer from security vulnerabilities.The Open Web Application Security Project (OWASP) is a nonprofit foundation that provides guidance on how to develop, purchase and maintain trustworthy and secure software applications. OWASP is noted for its popular Top 10 list of web application security vulnerabilities.Using Dependency-Check on a personal system
– Put the 'bin' directory of the dependency checker into the PATH environment variable of your system. – Make sure that Java is installed, and JAVA_HOME is set up properly. – Open a command prompt or terminal and run the following command: For windows: ./dependency-check.
What is vulnerability in OWASP : A vulnerability is a hole or a weakness in the application, which can be a design flaw or an implementation bug, that allows an attacker to cause harm to the stakeholders of an application. Stakeholders include the application owner, application users, and other entities that rely on the application.
How to use owasp dependency-check jenkins
The first step is to go to the Jenkins dashboard, select Manage Jenkins->Manage Plugins option, and install the OWASP Dependency-Check Plugin. The second step is to install the dependency-check tool from the Jenkins Global Tool Configuration under the System Configuration.
What is the difference between container scanning and dependency scanning : Dependency Scanning analyzes your project and tells you which software dependencies, including upstream dependencies, have been included in your project, and what known risks the dependencies contain. Container Scanning analyzes your containers and tells you about known risks in the operating system's (OS) packages.
The Open Web Application Security Project, or OWASP, is an international non-profit organization dedicated to web application security.
OWASP is an important and useful project for the security of web applications. OWASP offers a range of resources, standards, guidelines and tools to help protect web applications from the most common and dangerous attacks.
How do you check for unused dependency in your project
Identify Unused Dependencies
Use a tool like Depcheck to identify unused or unimportant dependencies in your project. Depcheck analyzes your project's package. json and can identify dependencies that are not imported or used in your code.The four main types of vulnerabilities in information security are network vulnerabilities, operating system vulnerabilities, process (or procedural) vulnerabilities, and human vulnerabilities.Vulnerability Scanning is an automated threat. The OWASP Automated Threat Handbook – Web Applications (pdf, print), an output of the OWASP Automated Threats to Web Applications Project, provides a fuller guide to each threat, detection methods and countermeasures.
The Open Worldwide Application Security Project (OWASP) is a nonprofit foundation that works to improve the security of software.
What language does Owasp dependency check support : Dependency-Check can be run as a command-line tool or integrated into a build system, and it supports a wide range of programming languages including Java, . NET, and Python.
Why scan containers for vulnerabilities : Container security scanning plays a crucial role in early vulnerability detection within the software development life cycle. By scanning images during the build phase, it preempts potential breaches and system compromises, addressing security issues before deployment.
What is the difference between vulnerability scanner and SIEM
Relationship Between SIEM and Vulnerability Management Tools
While SIEM focuses on real-time monitoring and threat detection, Vulnerability Management Tools concentrate on identifying system weaknesses proactively.
OWASP will help your organisation to mitigate risk, as well as conduct threat modelling or architectural threat analysis and is therefore an important resource to network and build your security expertise.Is OWASP still relevant The most recent OWASP Top 10 was released in 2021. Before this, there had not been a substantial update since 2017. While there have been several significant security developments since then, the 2021 edition remains relevant and well-respected in cybersecurity.
Why remove unused dependencies : Why: Removing project references that have no usage can help save space and reduce startup time of your application, because it takes time to load each module and avoids having the compiler load metadata that will never be used.