Antwort What is the use of service account? Weitere Antworten – What are service accounts used for
Service accounts are often created to run various applications, services, or automated processes within an organization's network. These accounts are typically granted high access privileges to perform their designated tasks, such as accessing databases, network shares, or critical systems.One of the greatest advantages of service accounts is automation: they are designed to access resources and perform operations without the need for human intervention. This is useful for applications that require continuous monitoring, reporting, or data processing.SQL Server service accounts allow SQL Server to run with the rights and privileges assigned to the service account.
What is the difference between a service account and a normal account : Service accounts are not associated with any human identity. A user account is an account tied to a human identity. A standard user account represents a human identity and typically has an associated password to prevent authorized access.
Are service accounts safe
Service account sprawl is associated with some bad security habits. There are several reasons why service accounts can get out of control and end up putting companies at risk of a compromise. Typically, IT admins are too busy or lack the proper mechanisms to properly record why a specific service account exists.
What is service account in layman terms : Service accounts are a special type of non-human privileged account used to execute applications and run automated services, virtual machine instances, and other processes. Service accounts can be privileged local or domain accounts, and in some cases, they may have domain administrative privileges.
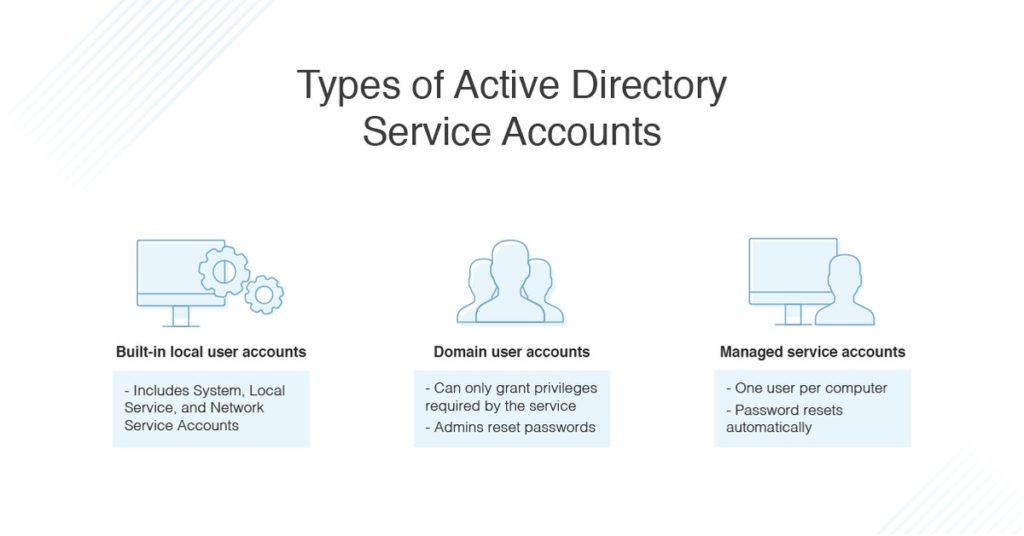
Service Accounts
These accounts are privileged local or domain accounts that are used by an application or service to interact with the operating system. Typically, they will only have domain access if it is required by the application being used.
It's a best practice to assign each service a separate account that is a member of a relevant security group. That way, even if the account for one service is compromised or damaged, other services will still operate normally. You can configure these permissions in Server Configuration Manager.
Why use service account impersonation
Service account impersonation is useful when you need to do tasks like the following: Grant a user temporary elevated access. Test whether a specific set of permissions is sufficient for a task. Locally develop applications that can only run as a service account.With limited options for managing service accounts, many organizations have developed poor security credential practices such as:
- Giving excessive privileges, or overprivileged service accounts.
- Failing to rotate or change service account passwords.
- Leaving default passwords in place.
The owner is the individual who will configure the application or applications to use the account; that is, the person who needs to know the ID and password for the Service Account. Their responsibilities include: Ensuring that there's a record of the process or application that uses the account.
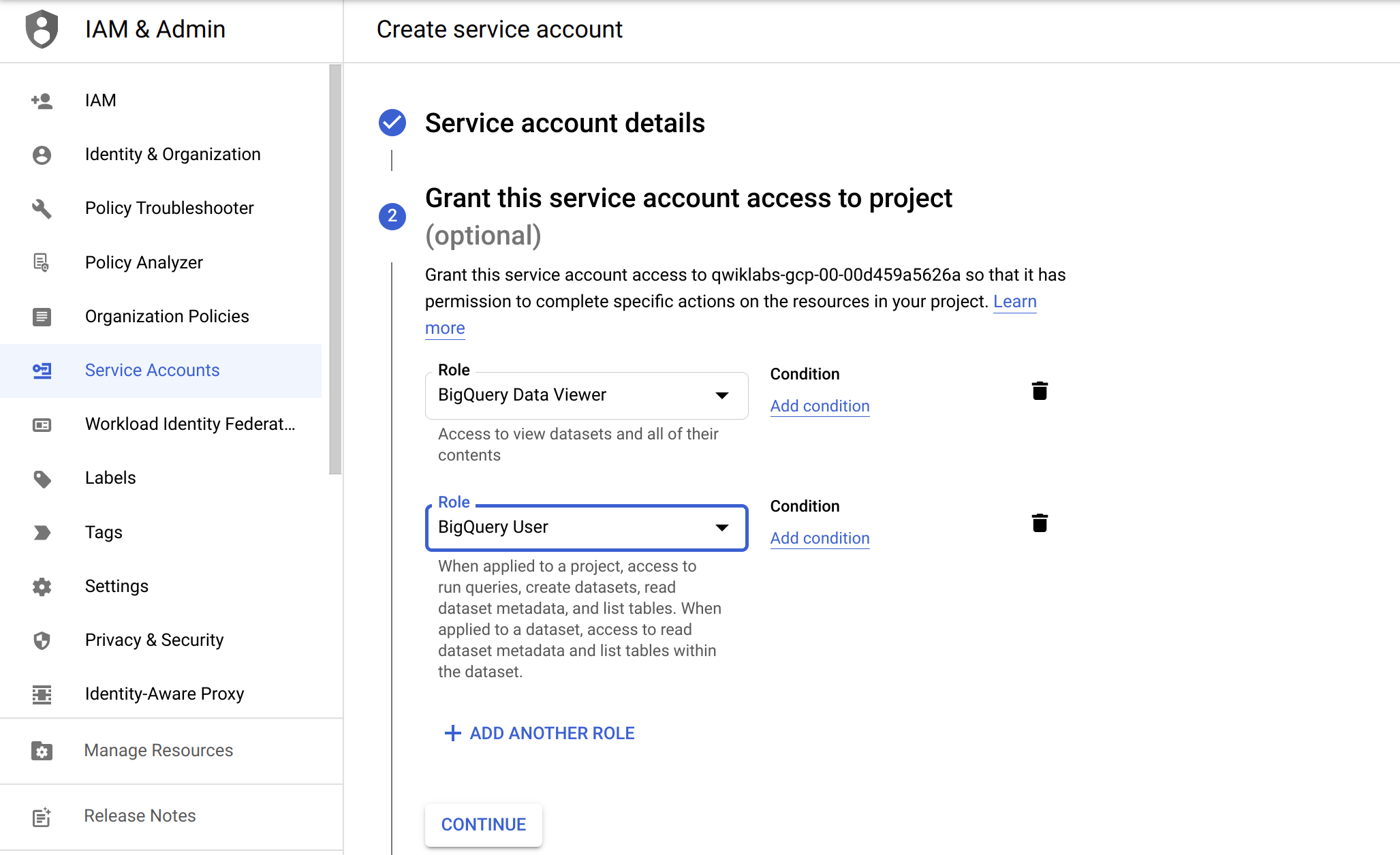
A service account is a special Google account that belongs to your application or a virtual machine (VM) instead of an individual end user. Your application uses the service account to call the Google API of a service, so that the users aren't directly involved.
What are service accounts and why are they a vulnerability : A service account is an account used to run services or applications, rather than being used interactively by administrators or business users. Service accounts often have privileged access to computers, applications and data, which makes them highly valuable to attackers.
What type of account is services : Service revenue is an account that is used to record the total amount of money received from providing services and is typically considered an operating expense, not a permanent account.
How to tell if an account is a service account
You can identify a managed service account by its distinguished name, GUID, security identifier (SID), or Security Account Manager (SAM) account name.
This page describes how each type of service account is created and used.
- User-managed service accounts.
- Google-managed service accounts.
- Service-specific service agents.
- Google APIs Service Agent.
- Role manager for Google-managed service accounts.
- What's next.
What is more, domain accounts can be used across multiple servers and can be easily reassigned to different servers if needed, providing flexibility in managing your SQL Server environment. Let's talk more about local accounts.
How to create a service account in SQL : Create the Account in SQL Server
Right-click Logins and select New login. Enter a Login name and select SQL Server Authorization. Enter and confirm a password. Configure the user as desired and click OK.